SIEM / SOAR log analysis software
Log analysis software for network and infrastructure security monitoring.
Partners

IT Security
Data Security
SIEM / SOAR – log analysis and incident response software
SIEM (Security Information and Event Management) is advanced software used for central collection, correlation, and analysis of security logs, as well as supporting SOC teams in incident response. Combined with a SOAR (Security Orchestration, Automation, and Response) module, it enables the automation of defensive actions, reducing response times and minimizing the risk of security breaches.

How does SIEM / SOAR software work?
The system is powered by data streaming from all security systems and devices operating within the organization’s IT ecosystem. The SIEM system processes data from:
- storage arrays,
- all log-generating and log-storing solutions (e.g., AD/Windows, antivirus systems, EDR, IPS/IDS systems)
- internal utility systems,
- servers,
- UTM / NG Firewall,
The collected data is analyzed by the system. SIEM uses advanced algorithms to correlate and analyze information, searching for patterns and anomalies that may indicate potential security threats.
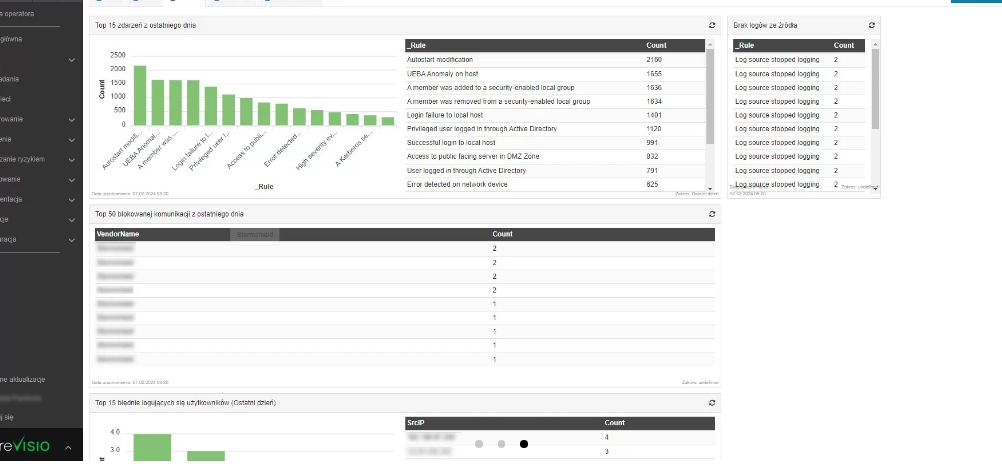
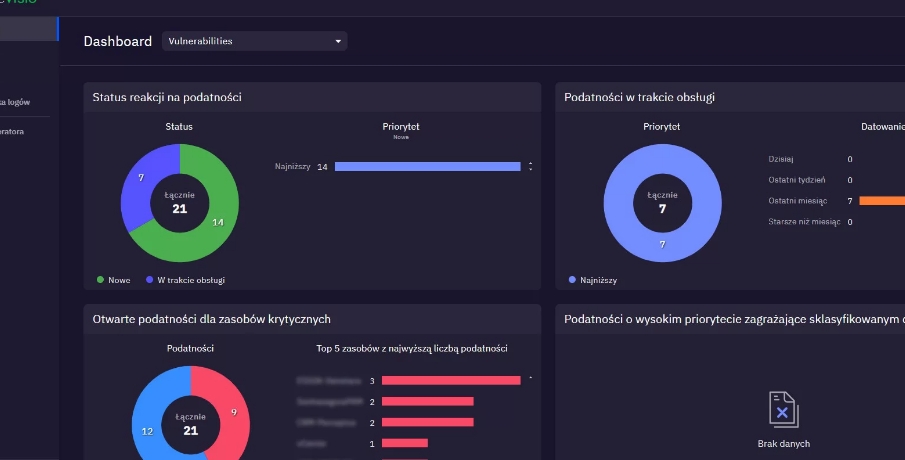
Detected anomalies generate alerts, providing the security team (SOC) with information about a possible incident. The system can also generate reports and dashboards to help analyze security trends. Furthermore, it supports the organization in managing compliance with legal regulations and conducting vulnerability audits.
Data normalization and correlation from diverse sources
Devices generate logs in their own specific formats. There is no universal model—data from an EDR system monitors differently than a UTM, and Windows logs look entirely different again. For this reason, identifying and converting them into a format that allows for comparing results across different sources (correlation) is extremely difficult. In any organization’s IT system, thousands of such logs are generated daily.
Prioritization of incidents and vulnerabilities
SIEM/SOAR aggregates logs from various devices into a single console. It enables their correlation and – with proper implementation, testing, and a “learning phase” within a specific unit – performs automated log analysis. It suggests to the operator which security events identified across various collectors are critical and require immediate attention, which are suspicious, and which – based on previous experience – appear to be safe.
Operator access via SIEM / SOAR console
An operator can manage all areas from a single console, gaining access to specific network segments (e.g., UTM) and making changes directly within the SIEM/SOAR environment.
Are you looking for a solution to support your security team? Fill out the form or contact our product manager!

FAQ – Frequently Asked Questions about SIEM/SOAR
What is the difference between SIEM and SOAR?
SIEM collects, normalizes, and analyzes logs, while SOAR adds incident response automation.
Can SIEM be implemented in a small company?
Yes – there are scalable solutions tailored to the size and budget of any organization.
How does SIEM help with GDPR and NIS2 compliance?
It ensures full event traceability, generates reports, and supports security audits.
How long does a SIEM implementation take?
From a few weeks to several months – depending on the infrastructure size and the number of integrations.
Does SIEM work in the cloud?
Yes – solutions are available on-premise, in the cloud, or in a hybrid model.
Consulting
We will help you choose the right solution.
Training
We offer training on hardware and software usage.
Implementations
We conduct comprehensive IT implementations.
Looking to enhance your cybersecurity?
Contact us!
Leave your details – we’ll call you back
Our specialist will get back to you no later than the next business day. You don’t have to fill in the message field, but a brief note about the topic you’re interested in will be a valuable hint for us.



