XDR and endpoint protection
CrowdStrike Falcon
IT Security
Data Security
Ransomware attacks can encrypt data within minutes; a traditional antivirus has long been insufficient. Your company needs a solution that sees more, reacts faster, and does not slow down your team’s workflow. As Perceptus, we provide CrowdStrike Falcon technology in Poland – the global market leader in XDR (Extended Detection and Response) solutions.
We combine Global Threat Intelligence with local implementation support.
Why is traditional antivirus not enough?
When managin IT security, companies face several critical challenges:

73% of SMBs experienced breaches in 2023. Traditional antiviruses relying on known attack patterns are helpless against new, unknown threats (Zero-Day).

The IT team is drowning in false alarms, wasting time verifying threats that do not exist.

„My computer is lagging”. Employees complain about performance drops during system scans or virus database updates. This translates into the cost of wasted time.

Cybercriminals increasingly steal identities (login/password) and simply log in. The antivirus won’t notice a thing because there is no malicious file involved.
What is XDR (Extended Detection and Response)
XDR (Extended Detection and Response) is the evolution of security that goes far beyond protecting just the computer. The integrated platform automatically collects and correlates data from multiple security layers:
- endpoints (laptops/servers)
- cloud
- network
- user identities
Simply put: Traditional security systems operate in silos. The antivirus sees the virus, the firewall sees network traffic, but they do not “talk” to each other. XDR connects these dots, seeing the full picture of the attack. This allows it to detect threats that remain entirely invisible to individual tools.
How does an XDR solution work in practise?
XDR-class solutions allow you to analyze data from the infrastructure and focus on the dangerous touchpoints between the user and the external network (email, browser, etc. ). Your IT department is no longer bombarded with thousands of unrelated security alerts.
If an employee clicks on a phishing link (email layer), leading to the compromise of their login credentials (identity layer), and the system detects an attempt to mass-download data from the server (network layer) – the XDR solution will semlessly combine these three events into one single incident. It will automatically block the account and cut off access to files at every stage of the attack.
Why does your company need XDR in 2026?
Implementing XDR is a shift in defense philosophy that brings tangible business benefits to your organization:
Faster detection and response (MTTD/MTTR)
XDR skraca czas potrzebny na wykrycie i zatrzymanie włamania (z tygodni do minut). W walce z ransomware każda sekunda decyduje o tym, czy stracisz dane.
Protection against identity theft
Most breaches no longer start with a virus, but with a stolen password. XDR detects unusual activity even on legitimate employee accounts.
Relieving the IT team
Thanks to automated event correlation and the reduction of false positives, your team doesn’t waste time “chasing ghosts” and can focus on real threats.
Regulatory compliance
XDR provides detailed logs and incident reporting. This is crucial for meeting legal requirements (NIS2, GDPR) regarding breach notification.
How is XDR different from antivirus?
Traditional antivirus was created in times when the main threats was a malicious file from another device or downloaded from the web. Current attacks are multi-stage. XDR is an advanced analytical platform that correlates data from the entire IT environment to provide a complete, real-time threat picture.
| Traditional antivirus | XDR system (CrowdStrike Falcon) | |
| Detection method | Signature-based (recognise only known viruses). | Behavioral analysis and AI (detects intentions and new Zero-Day attacks). |
| Scope of protection | Protects only the device it is installed on. | Entire IT environment (endpoints, identity, network, cloud). |
| Fileless attacks | Does not detect attacks using legitimate system tools. | Full protection (analyzes processes in memory and system commands). |
| Incident response | Simple deletion or quarantine of the infected file. | Remotely isolated the PC from the network, deletes files, and "kills" hacker processes. |
| Analysis & investigation | None. Only informs: "Virus removed/blocked". | Full context. You see exactly how the hacker entered, what they did, and what data they targeted |
| Performance impact | Requires frequent disk scans and database updates, slowing down devices. | Background agent. Analysis takes place in the cloud, without burdening the CPU. |
CrowdStrike Falcon: Technology that outpaces hackers
CrowdStrike is the global leader in Endpoint Protection, consistently recognized in Gartner and Forrester reports.
Discover the CrowdStrike Falcon platform, designed to outpace and predict the attackrs’ moves, rather than treating systems after an infection.
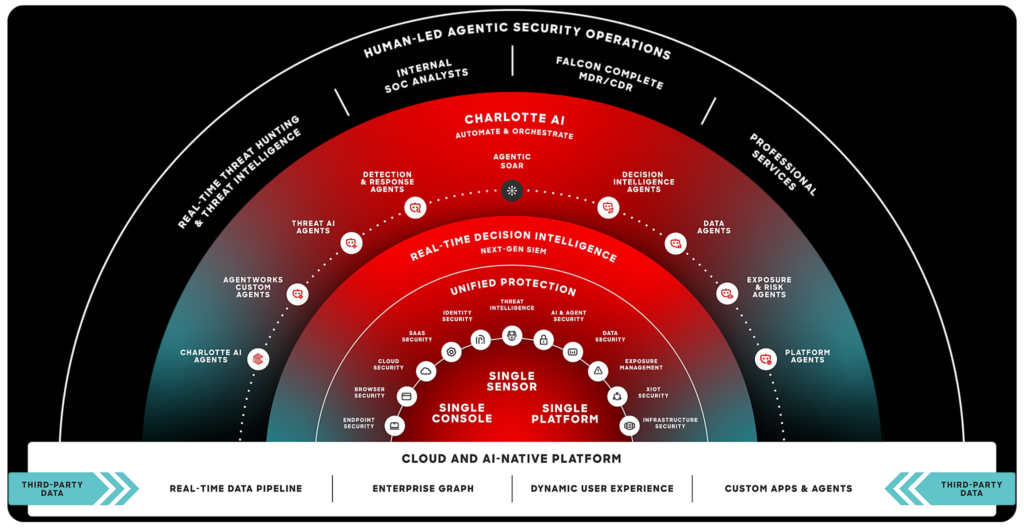
Built from the ground up in the cloud, is uses artifical intelligence to analyze behavious and stop attacks.
To win the race against cybercriminals, you need an experienced partner on your team. Perceptus engineers will ensure that the CrowdStrike Falcon platform is integrated with your infrastructure quickly and precisely.
CrowdStrike Falcon business benefits
Find out how the CrowdStrike Falcon platform will take your company’s security to the next level.
One, Ultra-light Agent
Forget about installing separate programs for antivirus, EDR, and USB control. Just one small sensor that installs in a minute, requires no system reboot, and consumes a minimal amount of resources.
Offline and Online Protection
Powered by built-in artificial intelligence (AI), the sensor keeps the employee safe even when they are offline.
The 1-10-60 Rule
Built for extreme speed: 1 minute for detection, 10 minutes for analysis, and 60 minutes for threat elimination.
How CrowdStrike Falcon protects company data
Antivirus programs rely on a database of attack patterns, acting like a digital wanted poster. Today, this approach is doomed to fail. The CrowdStrike Falcon platform completely redefines defense by focusing on behavioral analysis and AI.
Hackers don’t break in, they walk through the front door (they log in)!
If a criminal steals an employee’s password, they look like a legitimate user. CrowdStrike creates a map of emloyee behaviours. When the system detects an anomaly – e.g., logging in at an unusual time, from a strange location, or attempting “lateral movement” to servers with sensitive data – it will automatically force additional verification or completely cut off access.
100% effectiveness against ransomware
Digital extortionists have no chance to encrypt your drives. The Falcon platform analyzes every code and file exactly at the moment it tries to save to the disk or launch a process in the OS, neutralizing malicious processes before they can execute even a single operation. CrowdStrike regularly achieves the highest effectiveness in ransomware prevention in independent tests (SE Labs).
Cloud protection powered by Artificial Intelligence
CrowdStrike Falcon został was designed from the ground up in the cloud. It doesn’t just “use the cloud” – it lives in it.
- CrowdStrike Threat Graph – a global neural network that processes trillions of system events daily. It relies on collective immunity: if a client (e.g., a bank in Japan) is attacked with a new technique, the Threat Graph learns this pattern in real-time. Your company is automatically immunized against the same attack instantly.
- Charlotte AI – Crodwstrike’s Generative AI allows analysts to ask complex questions in natural language. Charlotte AI automates log analysis, significantly reducing investigation time.
The system is designed to win the race against the “breakout time” (the time a hacker takes to move from a infected PC to the rest of the network). Statistics show that CrowdStrike’s average Mean Time to Detect (MTTD) is just 4 minutes.
Explore CrowdStrike Falcon packages for organizations
Is a basic level of security enough for you? Or do you need advanced functionalities to tailor the solution strictly to your organization’s requirements? Not a problem! Explore the modules available across the CrowdStrike’s packages and see what they offer.
| Falcon Pro |
Falcon Enterprise |
Falcon Elite |
Falcon Complete Next-Gen MDR |
|
| Falcon Prevent Next-generation antivirus |
||||
| Falcon Device Control USB device control |
Add-on | |||
| Falcon Firewall Management Host firewall control |
||||
| Falcon Adversary OverWatch Threat hunting & intelligence |
Integrated intelligence |
|||
| Falcon Insight XDR Detection & response |
||||
| Falcon Discover IT hygiene |
||||
| Falcon Identity Protection Identity protection |
Add-on | |||
| CrowdStrike Services Express support |
Add-on | Add-on |
Your security with professional support from Perceptus
Buying a license is only half the battle. Enterprise-class technology requires proper configuration to serve your business, not block it.
In a cooperation model with Perecptus you receive:
Adaptation to realities: We help implement security policies compliant with your specific operational environment and legal requirements (e.g., NIS2, GDPR).
Quick Implementation: Thanks to our vast experience, the CrowdStrike Falcon installation proceeds without disrupting your company’s workflow.
Technical Support: Got a problem? Call your designated Perceptus engineer who knows your infrastructure inside out. You won’t have to wait on the global vendor’s hotline.
Security Audit: Before implementation, we assess your environment to eliminate potential conflicts and vulnerabilities.
Ready to deploy the global leader in XDR – Crowdstrike Falcon with Perceptus?
Contact us, we will be happy to help!
Consulting
We will help you choose the right solution.
Training
We offer training on hardware and software usage.
Implementations
We conduct comprehensive IT implementations.
Looking to enhance your cybersecurity?
Contact us!
Leave your details – we’ll call you back
Our specialist will get back to you no later than the next business day. You don’t have to fill in the message field, but a brief note about the topic you’re interested in will be a valuable hint for us.






