MDR for ESET
Partners

IT Security
Data Security
24/7 Monitoring and Response
- your organization’s security in the hands of experts.
Is your ESET Inspect truly protecting you?
You have ESET Inspect – that is a great step toward security. But are you utilizing its full potential?
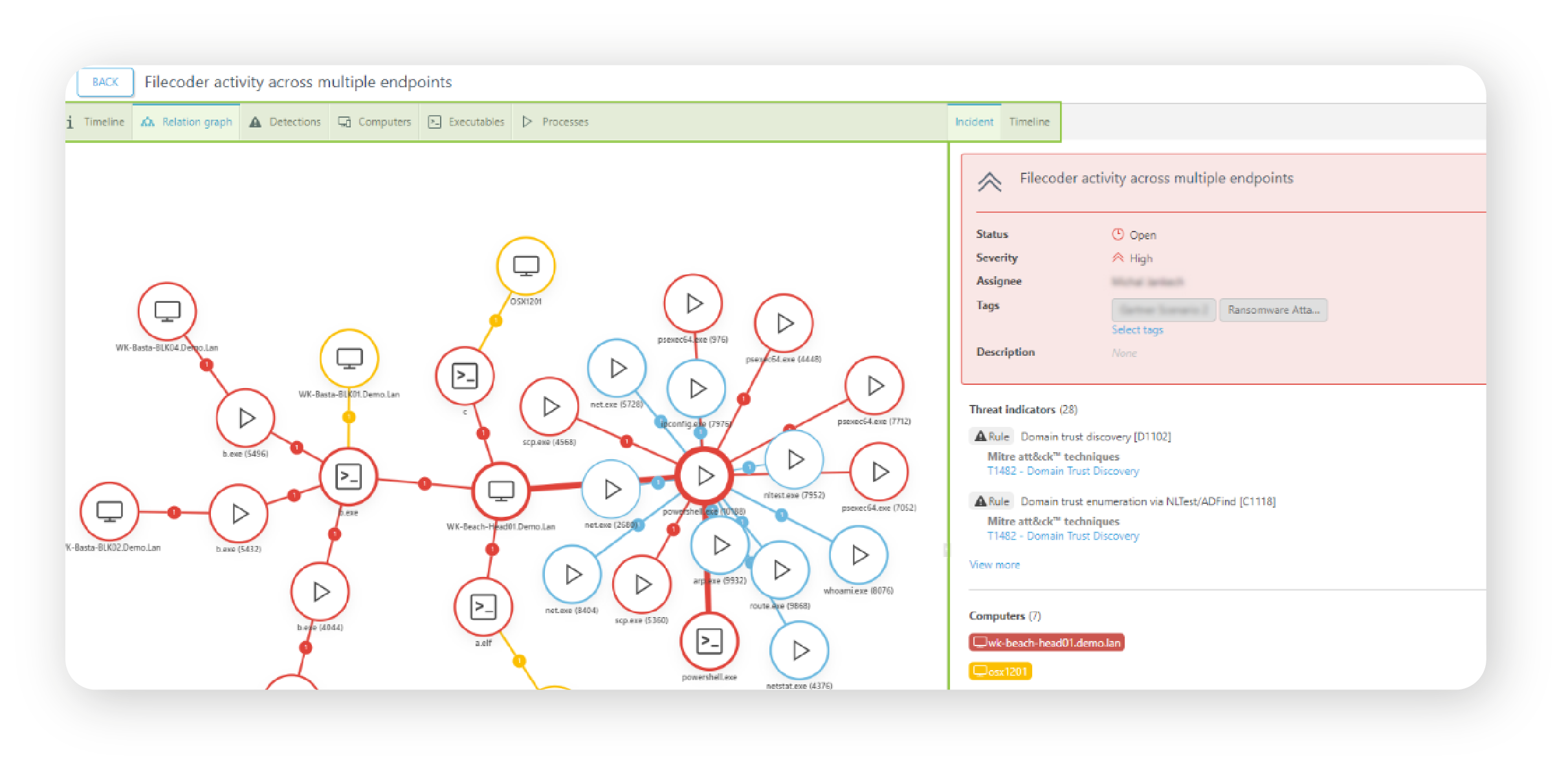
Attackers rarely start with obvious malware. Instead, they use tools that are part of the daily routine for administrators and users. Consequently, the early stages of an attack can go unnoticed if no one is regularly analyzing alerts and hunting for unusual behavioral patterns.
- PowerShell – used by admins for automation, but also by attackers to download and execute malicious code in memory, bypassing traditional antivirus.
- PsExec – an excellent tool for remote command execution, but often repurposed for lateral movement across a network.
- RDP (Remote Desktop Protocol) – essential for remote work, yet a favorite method for attackers to hijack systems.
- Mimikatz – a tool used by admins for security testing, but in the hands of attackers, it serves to steal passwords and access tokens.
- Macrobased attacks (VBA, Excel Macros) – office macros are powerfull automation tools that can be weaponized to deliver malware, particulary in phishing campaigns.
Imagine these scenarios:
An accountant who has never used PowerShell suddenly runs a script downloaded from an external server. A regular administrator might overlook this – after all, PowerShell is a standard system tool. But someone who knows attack patterns recognizes this as a classic Living Off The Land (LotL) technique, where the attacker uses legitimate tools to hide their tracks.

Someone logs in via RDP in the middle of the night. Is it an administrator or a compromised account? Without context, such events can go unnoticed for weeks until the attack reaches its next phase – file encryption or data exfiltration.
If you aren't analyzing these events daily, you won't notice the threat until it’s too late.
Your Mini Security Operations Center
Our MDR (Managed Detection and Response) service was created specifically to help you get the most out of your existing security stack. It provides round-the-clock supervision and rapid threat response. Our certified engineers, who possess deep expertise in ESET Inspect, monitor your IT environment 24/7/365, analyzing events and responding to any suspicious activity.
We do not act chaotically – response scenarios are developed in advance and implemented immediately when the situation demands it. If something unusual arises, we contact your company’s designated representative to make the best decision together.
This isn’t just protection against attacks – it’s the full utilization of the ESET Inspect potential you already have.
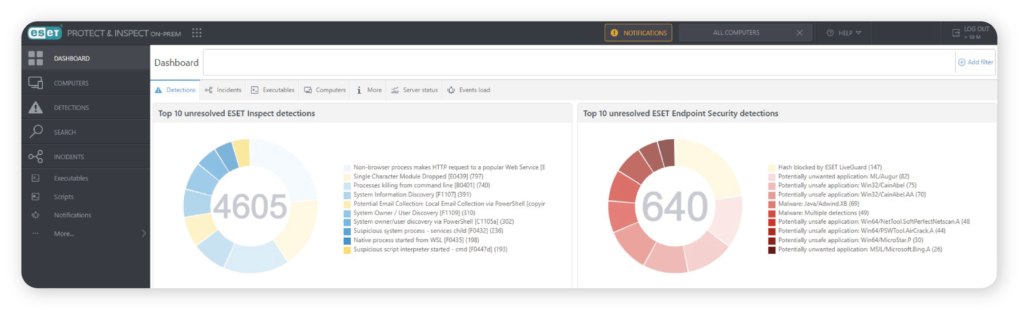
Scope of the MDR for ESET Inspect Service
24/7 Monitoring and Threat Response – Constant analysis of your network activity.
Rapid Cyberthreat Elimination – Neutralizing threats before they cause damage.
Root Cause Analysis (RCA) – Ensuring the attack does not recur in the future.
Regular Cybersecurity Reports – Full transparency of all activities.
Monthly Technical Meetings – Discussing completed work and recommending improvements.
Containment of Attack Spread – Detecting and isolating threats at an early stage.
Continuous Security Rule Updates – Constant optimization of your defenses.
ESET Inspect Console Management – Maximizing its built-in capabilities.
MDR – security that actually works
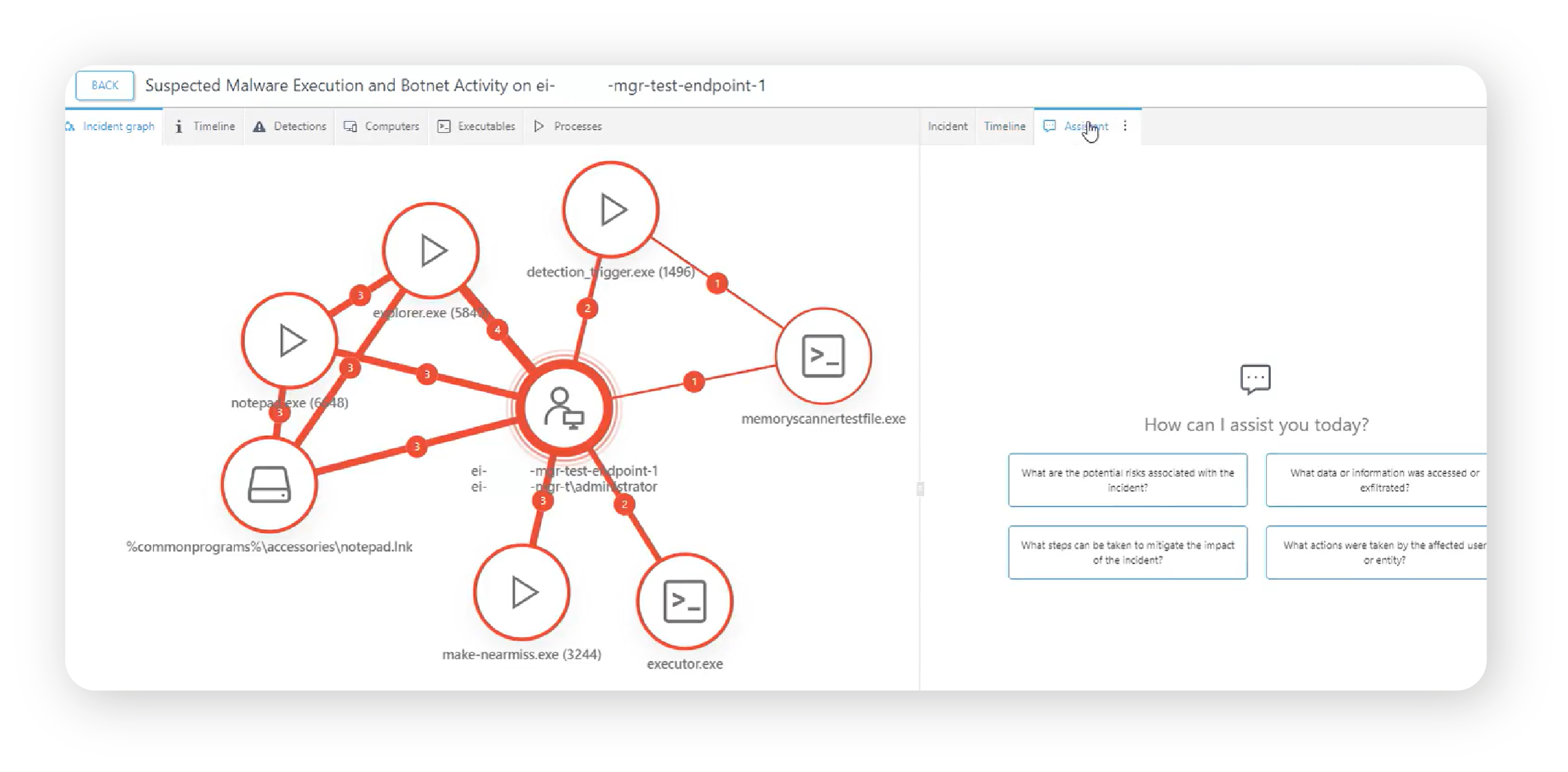
Too many companies only find out about an attack when it is already too late. Don’t let your organization be one of them. With our MDR service, your security is in the hands of specialists watching over you 24/7.
Consulting
We will help you choose the right solution.
Training
We offer training on hardware and software usage.
Implementations
We conduct comprehesive IT implementations.
Looking to enhance your cybersecurity?
Contact us!
Leave your details – we’ll call you back
Our specialist will get back to you no later than the next business day. You don’t have to fill in the message field, but a brief note about the topic you’re interested in will be a valuable hint for us.


