EDR & Endpoint Protection Systems
Corporate antivirus software. System implementation and integration. Protection against viruses, ransomware, and malware with ESET solutions for business.
Partners

IT Security
Data Security
Looking to use a simplified procedure to order software for your public administration unit via the COAR platform?
Endpoint Protection Software
Endpoint Protection solutions safeguard endpoints such as desktops, laptops, smartphones, and other devices connected to the corporate network.
This concept encompasses a set of technologies and processes designed to protect end-user devices from cyber threats.
Choose the right bundle
| Bundle Content |
PROTECT ENTRY | PROTECT ADVANCED | PROTECT COMPLETE | PROTECT ENTERPRISE | PROTECT ELITE |
|---|---|---|---|---|---|
| ESET PROTECT Cloud Console | |||||
| ESET PROTECT Console | |||||
| ESET Server Security / ESS | |||||
| ESET Endpoint Antivirus EEA | |||||
| ESET Endpoint Security for Android / EES AND | |||||
| ESET Endpoint Security / EES | |||||
| Cloud Sandboxing / ELGA | |||||
| Full Disk Encryption / EFD | |||||
| Mail Server Security / EMS | |||||
| Microsoft 365 Protection / ECO & ELGA | |||||
| Vulnerability & Patch Management | |||||
| Extended Detection & Response / EI | |||||
| Multi-Factor Authentication / 2FA |
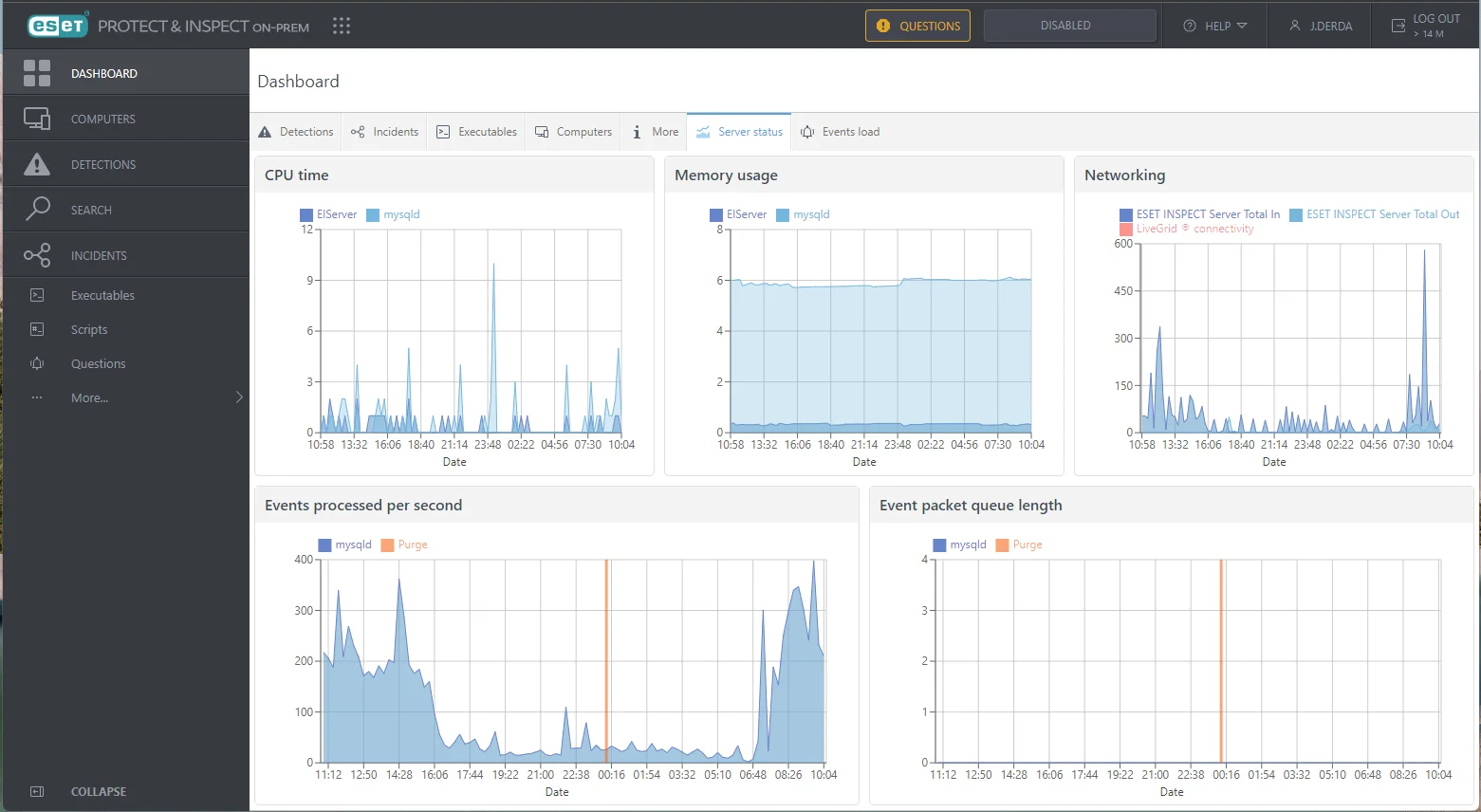
EDR available in ESET software
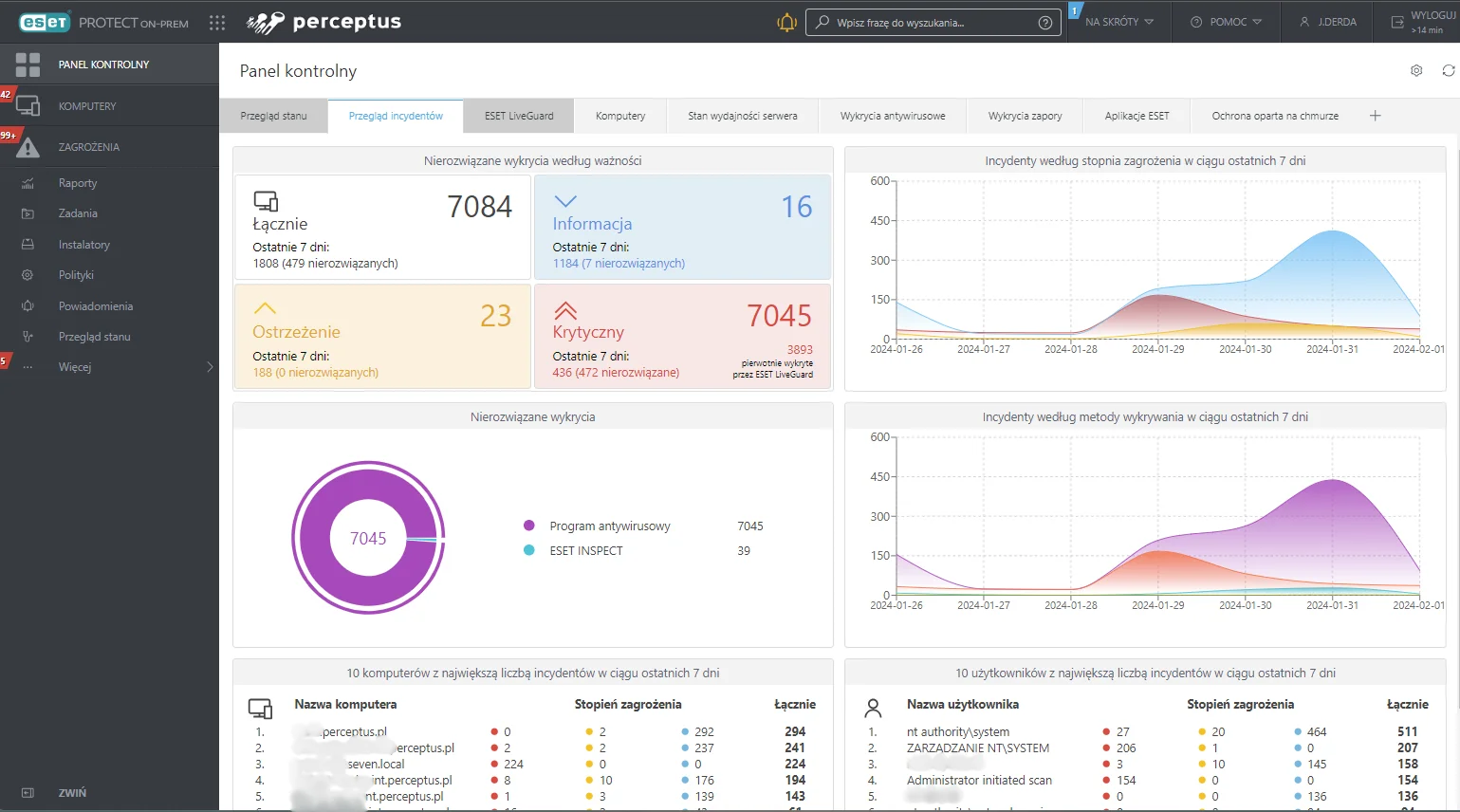
ESET Extended Detection & Response (EDR) is an advanced IT security tool that enables organizations to detect, monitor, and respond to advanced threats across various network points.
Compared to traditional antivirus solutions, ESET EDR:
offers extended functionality,
enables more effective tracking and response to security incidents,
Integrates various data sources, such as endpoint data, event logs, and user behavior information, providing a more comprehensive and holistic approach to cyber protection.
Advanced security features
ESET Vulnerability & Patch Management
Allows organizations to effectively manage vulnerabilities and updates. This tool identifies and classifies potential security gaps in operating systems, applications, and network devices. It also enables automatic deployment of updates and security patches, minimizing the risk of attacks and security breaches.
ESET 2FA (Multi-Factor-Authentication)
An additional security layer requiring users to provide a unique code to confirm their identity when logging into systems or applications. This second factor, generated via a mobile app, hardware token, or SMS, prevents unauthorized access even if a password is compromised.
ESET Cloud Office Security
Provides comprehensive protection for cloud-based office environments, such as remote work platforms and email services. It offers advanced protection against phishing, malware, ransomware, and other malicious attacks while ensuring data integrity in cloud environments.
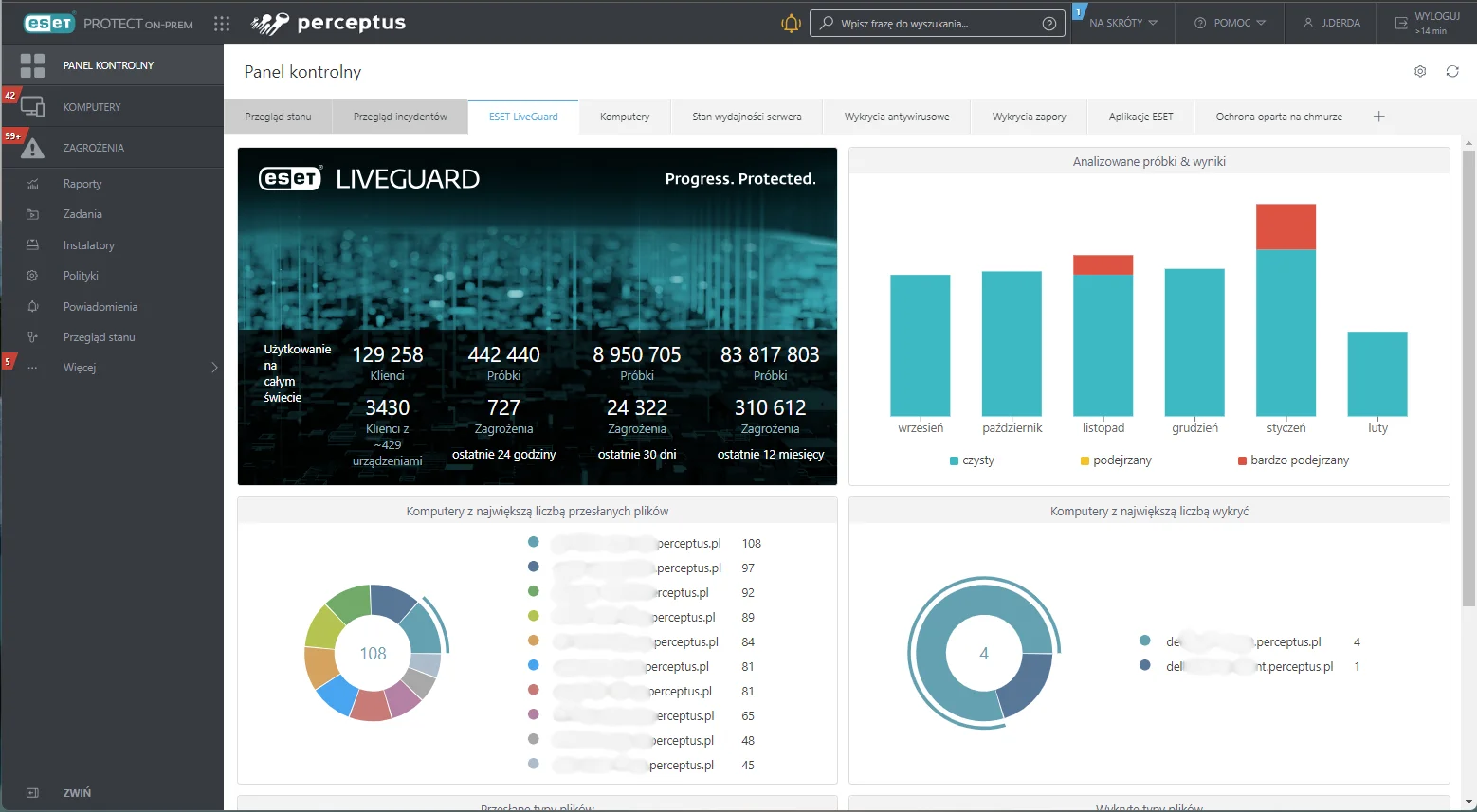
ESET LiveGuard
Adds a cloud-based protection layer designed to mitigate “zero-day” threats (threats never seen before).
ESET LiveGuard is based on:
local threat remediation,
sandboxing
cloud analysis,
proactive protection,
In the ‘Submitted Files’ section of the remote management console, administrators receive a brief behavioral report for each submitted sample.
If a file proves to be malicious, it is marked as a suspicious object and blocked for all users participating in ESET LiveGrid®. If a file is assessed as suspicious, it will be blocked on all computers within the user’s organization according to the configured sensitivity threshold.
Application of ESET LiveGuard
Suspicious samples that have not yet been confirmed as malicious and potentially contain malware are automatically submitted to the ESET cloud. These submitted samples are executed using sandboxing and analyzed by advanced malware detection engines.
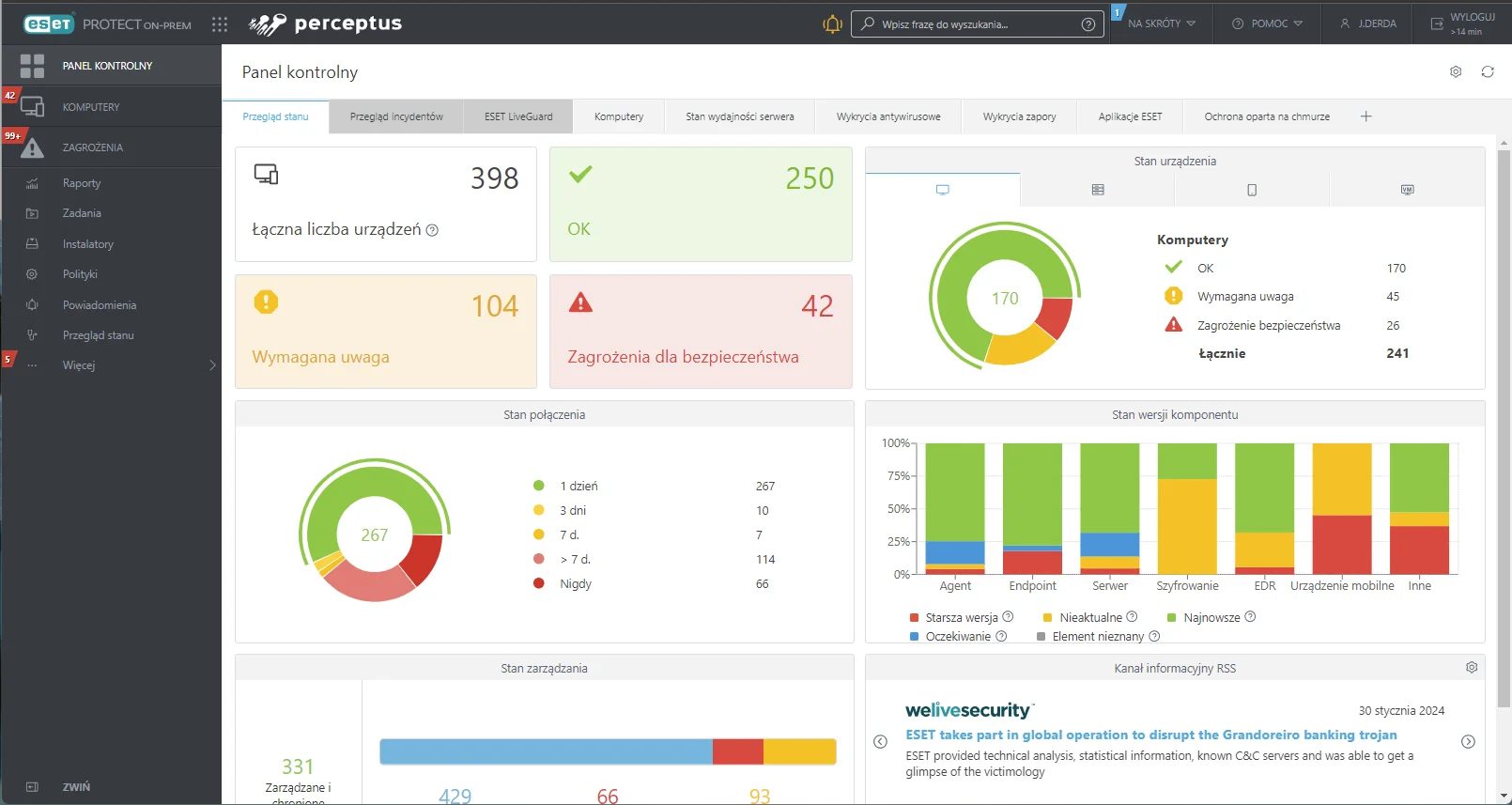
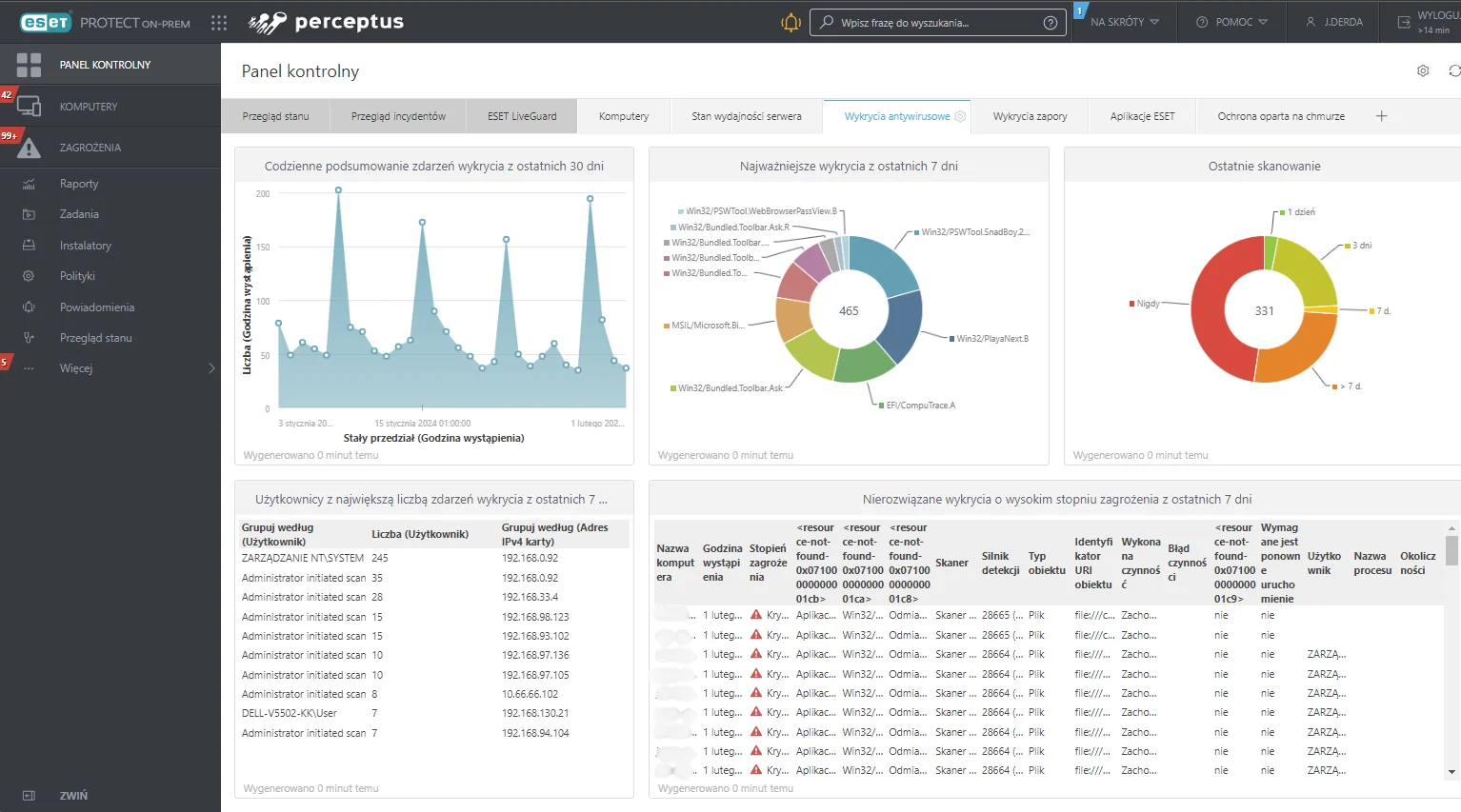
Comprehensive ESET Endpoint Protection implementation
The Perceptus engineering team has years of experience implementing endpoint protection solutions and providing training on their optimal use.
Looking for a solution tailored to your enterprise? Contact us and leverage our long-standing expertise to guide you through the entire implementation process.
FAQ – Frequently Asked Questions about Endpoint Protection
How does Endpoint Protection differ from traditional antivirus?
Traditional antivirus focuses on detecting known threats. Endpoint Protection includes proactive defense, vulnerability management, behavioral analysis, and data encryption.
Does ESET Endpoint Protection work in the cloud?
Yes – the ESET PROTECT Cloud console enables remote security management for all devices within the organization.
Can ESET be deployed only on selected devices?
Yes – both licensing and deployment can be tailored to the actual needs of your company.
Does ESET protect against ransomware?
Yes – thanks to advanced detection, sandboxing, and behavioral analysis.
Strengthen your data protection! Free on-demand webinars
Understanding the benefits that endpoint protection tools provide beyond traditional antivirus is crucial.
To make this easier, we offer a series of free on-demand webinars. Upon registration, an access link is sent to your email address, allowing you to watch the material at any time.

- Endpoint Detection & Response (EDR) solutions – How to boost endpoint and server protection?
- Strengthen employee authentication – Multi-Factor Authentication for remote work.
- Cloud Migration – What does it look like and what are the benefits?
- ESET Vulnerability & Patch Management – Step-by-step setup and demo.
- Advanced XDR Management – Managing protection, vulnerabilities, and incidents.
Consulting
We will help you choose the right solution.
Training
We offer training on hardware and software usage.
Implementations
We conduct comprehensive IT implementations.
Looking to enhance your cybersecurity?
Contact us!
Leave your details – we’ll call you back
Our specialist will get back to you no later than the next business day. You don’t have to fill in the message field, but a brief note about the topic you’re interested in will be a valuable hint for us.



